Emerging security threats and attacks like unauthenticated network penetration, policy breaches, traffic flooding, and more have increasingly become common across global companies, leading them to substantial revenue losses. It’s critical to ensure your business doesn’t succumb to any intrusion attacks. An intrusion attack can cause serious damage to your networks and integrated systems.
To mitigate risks of unauthorized access to enterprise networks, the Intrusion Detection System (IDS) is an effective security solution. It proactively analyzes, detects, and alerts you to suspicious activities in your network. We’ll discuss everything about IDS, including its working mechanism, classification, and the best security software to help prevent malicious intrusion attacks.
What Is an Intrusion Detection System (IDS)?
A properly configured intrusion detection system (IDS):
- Monitors your inbound and outbound network traffic
- Continuously analyzes activity patterns
- Immediately alerts you to unusual behavior within the network
An IDS uses integrated intrusion signatures for identifying potential malicious activities capable of damaging your network.
Moreover, IDS is a technology or application built for securing networks from vulnerability exploits to provide you with the capability to quickly respond to and prevent spoofed, unauthorized network packets from infecting your target systems. An efficient IDS program logs all incoming and outgoing traffic, keeping an eye on information packets being transmitted across the network and issues an alert if the traffic deviates from the usual pattern. This way, you’re warned about potential intrusion threats early on, enabling you to respond to such threats proactively.
However, a misconfigured or an incompetent IDS also generates false alarms against some network traffic activity. It’s therefore essential to implement an advanced and intelligent software to extend your existing intrusion detection capabilities to intrusion prevention capabilities for end-to-end enterprise network security. Besides, you must also ensure your IDS is configured correctly within the networked systems. Before we jump to the evaluation of the best IDS software, let’s understand how a typical IDS works and what are the types.
How Does an Intrusion Detection System (IDS) Work? — The Mechanism Behind It
An intrusion detection system is a monitor-only application designed to identify and report on anomalies before hackers can damage your network infrastructure. IDS is either installed on your network or a client system (host-based IDS).
Typical intrusion detection systems look for known attack signatures or abnormal deviations from set norms. These anomalous patterns in the network traffic are then sent up in the stack for further investigation at the protocol and application layers of the OSI (Open Systems Interconnection) model.
An IDS is placed out of the real-time communication band (a path between the information sender and receiver) within your network infrastructure to work as a detection system. It instead leverages a SPAN or TAP port for network monitoring and analyzes a copy of inline network packets (fetched through port mirroring) to make sure the streaming traffic is not malicious or spoofed in any way. The IDS efficiently detects infected elements with the potential to impact your overall network performance, such as malformed information packets, DNS poisonings, Xmas scans, and more.
Types of IDS
Intrusion detection systems have four types based on the different mitigation techniques used to detect suspicious activities. Outlined below are the types of intrusion detection systems:
- Network Intrusion Detection System (NIDS) – Network IDS is deployed across your network infrastructure at specific strategic points such as the subnets most vulnerable to an exploit or attack. A NIDS placed at these points monitors the entire inbound and outbound traffic flowing to and from the network devices.
- Host Intrusion Detection System (HIDS) – On the other hand, Host IDS is configured in all the client computers (called hosts) running within your network environment. HIDS monitors the devices with access to your internal network and the internet. As it’s installed on networked computers, HIDS can detect malicious network packets transmitted within the organization (internally), including any infected host attempting to intrude into other computers. NIDS usually fails to do that.
- Anomaly-Based Intrusion Detection System (AIDS) – This type of IDS is based on a method or an approach where the program monitors your ongoing network traffic and analyzes its pattern against predefined norms or baseline. It then identifies and alerts the admins to unusual behavior across network bandwidth, devices, ports, protocols, etc.
Signature-Based Intrusion Detection System (SIDS) – These systems have an integrated database or library of signatures or properties exhibited by known intrusion attacks or malicious threats. Signature-based IDS monitors all the network packets and detects potential malware by analyzing if these signatures match the suspicious activities happening.
Best Intrusion Detection System for Preventing Security Attacks
SolarWinds offers Security Event Manager (SEM) with intrusion detection capabilities to help establish a correlation between intrusion detection alerts and event logs to gain complete visibility and control over your threat landscape.
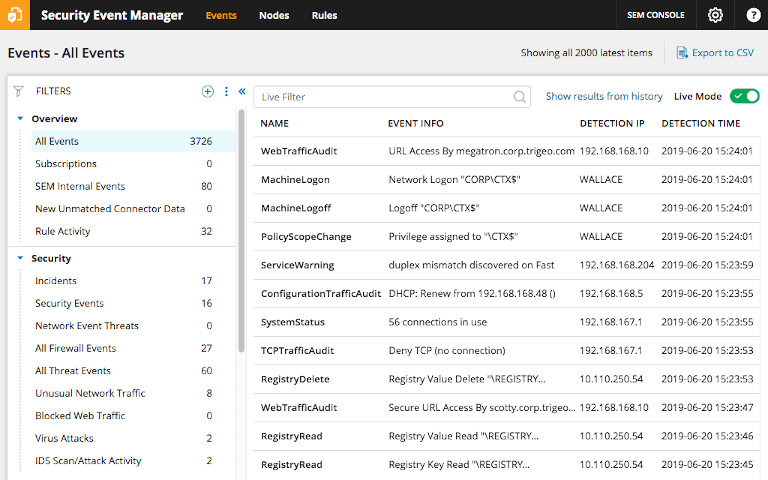
SEM collects and provides a centralized view of real-time event log data and analyzes the types and volume of attacks on your network to safeguard your infrastructure. It also fetches network activity details from multiple sources (your existing network intrusion detection systems, other infrastructure) and integrates them with event logs captured in the SEM dashboard, so you deploy informed responses to threats. Leveraging this information, you get a clear understanding of how prone your network is to intrusion threats, thereby improving your current intrusion detection systems and practices.
A Network Intrusion Detection System, combined with Security Event Manager, provides greater visibility into your network infrastructure, allowing you to use detailed log information for creating risk assessment reports and demonstrating compliance. SEM facilitates a wide array of customizable, out-of-the-box templates for easy, standardized reporting that makes sense to your stakeholders and auditors. It also allows you to schedule and share your reports with stakeholders/managers for review and approval processes.
Security Event Manager’s intrusion detection software/capability harnesses advanced technology to save you from putting manual efforts to monitor network traffic and perform mitigation tasks. The software continuously watches, identifies, and alerts on suspicious activities occurring within your network. Moreover, the active response capabilities enable the software to take automated actions against certain malicious events such as:
- Deploying network sensors for network intrusion detection
- Automating network asset discovery
- Analyzing data analysis
It not only reduces the manual efforts of your security personnel but also speeds up cyber threat identification and response. With SEM in place, you can proactively identify and eliminate malicious IPs, accounts, applications, and vulnerable network devices trying to intrude your environment. Get more information about this real-time intrusion detection and prevention system here.
