Amid predictions that 75.44 billion devices will have internet connectivity by 2025, IP address management has become a fundamental housekeeping and security concern for any networking admin. As the Internet of Things (IoT) continues to endow more and more devices with smart capabilities, networking grows more complex, making IP-centered network security measures a business imperative. With more devices comes more risk of networking complications and potential breaches—especially given the BYOD (Bring Your Own Device) trend, which allows employees to connect to company Wi-Fi via their personal mobile phones and laptops.
How to Find All IP Addresses on a Network
1. SolarWinds IP Address Manager (Free Trial)
4. Engineer’s Toolset (Free Trial)
5.SolarWinds Network Performance Monitor (Free Trial)
6. SolarWinds User Device Tracker (Free Trial)
The Importance of IP Addresses in Networking
Positioning Your Organization for Success
With the number of networked devices skyrocketing, network administrators must know how to scan their network for devices, track IP addresses, and perform IP address management. This guide describes how IP address scanners help empower IT departments to better track the many devices within a network, identify when IP addresses have been mislabeled or misallocated, and detect possible breaches, in addition to diving deeper into the why and how of IP address management from answering basic to advanced IP address strategies.
To maintain good network health and prevent unauthorized users from spying or wasting valuable bandwidth, admins are expected to not only know how to scan their network for devices but also understand the importance behind IP address management.
How to Find All IP Addresses on a Network
Knowing how to scan the network for devices is the first step, and one of the most fundamental, in managing IP addresses. When organizational members experience problems connecting their device to the network or the internet, having a full list of IP addresses on the network can guide administrators as they troubleshoot and restore order.
The most basic way to find all the IP addresses on a network is with a manual network scan. This method is best for those looking to perform a rapid, one-time device check or for those heading smaller organizations with a more manageable device list. To rapidly scan a network yourself using native operating system (OS) capabilities, follow these steps.
- Open the command prompt.
- Enter the command “ipconfig” for Mac or “ifconfig” on Linux. Your computer will then display its own IP address, subnet mask, gateway address, and more, making it possible for you to determine the network number you’ll be scanning. For example, in a Class C IPv4 network—which most small local networks are wont to be—you may find your computer’s IP address is, let’s say, 192.168.1.75. If the subnet mask is 255.255.255.0, then you know the first 3 bytes are the network ID (192.168.1) and your broadcast IP address is 192.168.1.255.
- Next, input the command “arp -a”. ARP stands for “Address Resolution Protocol,” and the “-a” appendage of the command prompts the device to list all the IP addresses found within the ARP cache for the associated network. In other words, the “arp -a” command displays all active IP addresses connected to the local network. This list is incredibly informative, containing the IP addresses, MAC addresses, and allocation type (whether static or dynamic) for all live hosts.
- Optional: Input the command “ping -t”. The “ping -t” command allows you to perform an extended ping on the list produced by the previous command, testing connectivity and latency within the network. This will enable you to further narrow down what devices could be experiencing or causing problems.
However, there are a few ways to scan local networks for IP addresses. Typically, the best way to find the IP addresses of all devices on a network is to invest in software. This is especially true for large organizations using dynamic IP addresses, in which case the large volume of networked devices and staggered address changes can quickly become overwhelming to track and organize. Using an IP address scanner, admins can see which addresses are active, which are free for reallocation, which might belong to unauthorized users, and which have perhaps been duplicated and caused collisions.
6 Best IP Scanners
While it’s possible to scan a network for active IP addresses using native commands, manually tracking the addresses of all networked devices can quickly become an outsized task for any one staff member. This is particularly true when you look at the data this method makes available to you. Yes, ipconfig displays the IP address of each active network device and its corresponding MAC address, but most IT members don’t happen to know the MAC address of every single computer within the network—that expectation would be unreasonable, if not impossible in larger networks. Suffice it to say, this information doesn’t exactly guide you to the root source of a problem or provide much network mapping. It merely enables you to identify IP addresses and spot possible duplicates or mismatches.
For this reason, downloading software with a fuller suite of IP address management (IPAM) services is highly recommended. To help you fill out your IPAM toolset, I’ve rounded up the six best network scanner and address management clients. While some are free, these are generally more supplementary tools. Cobbled together, a collection of standalone software can certainly yield powerful results.
In terms of expedient and comprehensive data consolidation, however, the best results tend to come from premium software. A completely integrated management tool—like the SolarWinds® IP Address Manager, the most robust IPAM software and my personal favorite—might have a higher price tag but ultimately pays for itself by automating rote tasks and performing insightful analysis, decreasing system downtime while increasing productivity and profit.
- SolarWinds IP Address Manager (Free Trial)
The preeminent full-service IP address mangement tool, SolarWinds IPAM goes far beyond the offerings of an IP address tracker. IPAM is a complete management solution, empowering admins to drill down into address conflicts, easily allocate IP addresses to subnets, and catalogue IP address usage history.
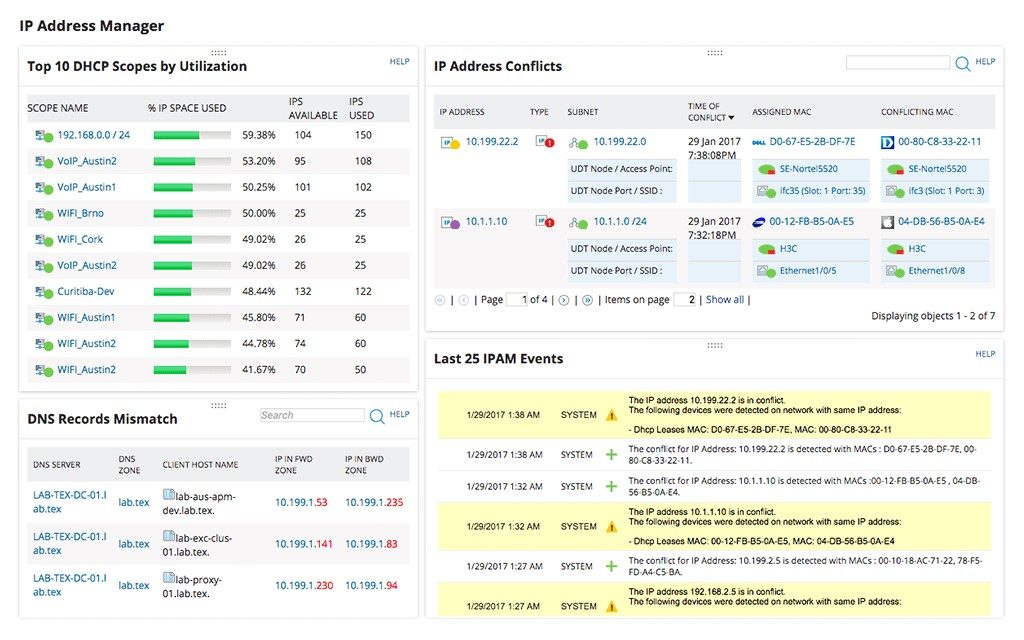
These functions are crucial time-savers. When alerted to a conflict, users can begin troubleshooting by viewing the event’s details, including the specific endpoints involved. This allows admins to temporarily remove the malfunctioning devices by remotely shutting down a port, thus facilitating network reliability and high performance while reconfiguring IP settings behind the conflict.
As regards address allocation, IPAM users can employ the automated Subnet Discovery Wizard and Subnet Allocation Wizard to sort IP addresses and form optimally sized subnets, maximizing performance while minimizing conflicts and wasted space. Better yet, IPAM features drag-and-drop and user-defined grouping, making portioning IP address space more convenient than ever before.
One last notable feature here is that it offers priceless server synchronization. This makes it possible not merely to set alerts for conflicts and put out fires as they arise, but to prevent potentially expensive address conflicts to begin with. IPAM integrates DNS server and DHCP server management in one console and supports multiple vendors. This means customers can find available addresses, assign them, and update the DNS simultaneously, eliminating the possibility of misdirected traffic or duplication.
2. Angry IP Scanner
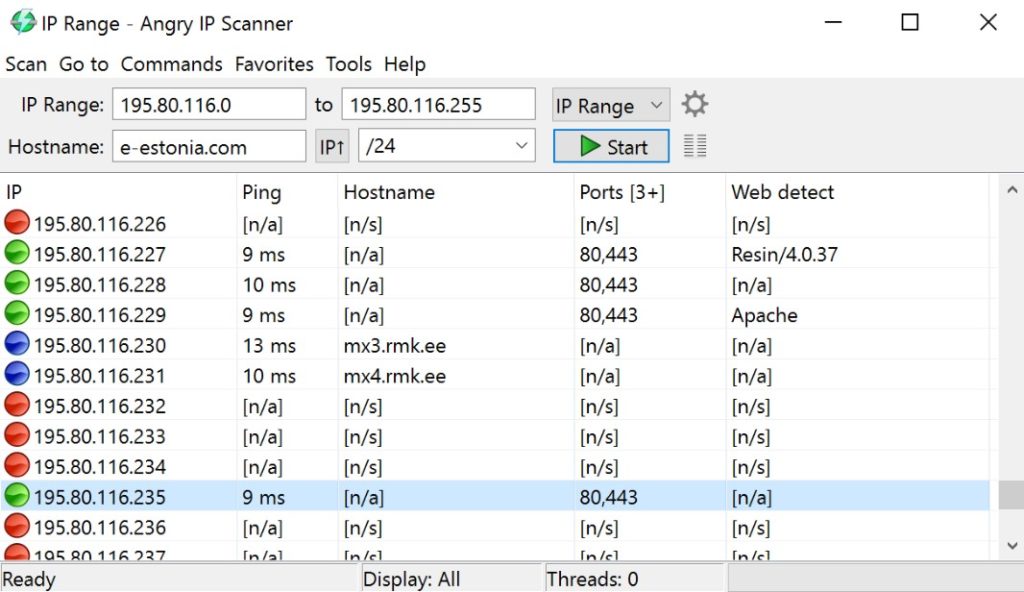
Widely hailed as one of the first and most popular free IP address scanners, Angry IP Scanner is open-source software, deployable across operating systems. Windows, Linux, and Mac OS X users will find this tool handy for its nonexistent price tag.
Angry IP Scanner is easy to use and has an intuitive graphical user interface. Further, it provides slightly more detail than the manual command-line method covered above. Given an IP address range, the tool displays all active IP addresses, hostname when applicable, ping response time, MAC address, and port count. These results are made actionable with an export function that supports CSV, TXT, XML, and IP-Port list files.
Additionally, Angry IP Scanner can display Network Basic Input/Output System (NetBIOS) information useful for identifying an IP address, as knowing the computer name or current logged-in user can facilitate network problem solving.
The main downside of Angry IP Scanner is the basic nature of its capabilities, which is understandable given that it’s open-source. The functionalities it offers are fundamental and useful. Plus, anyone who writes Java is free to expand its abilities by creating their own plugins, though of course this would require a certain amount of buy-in.
3. IP Scanner
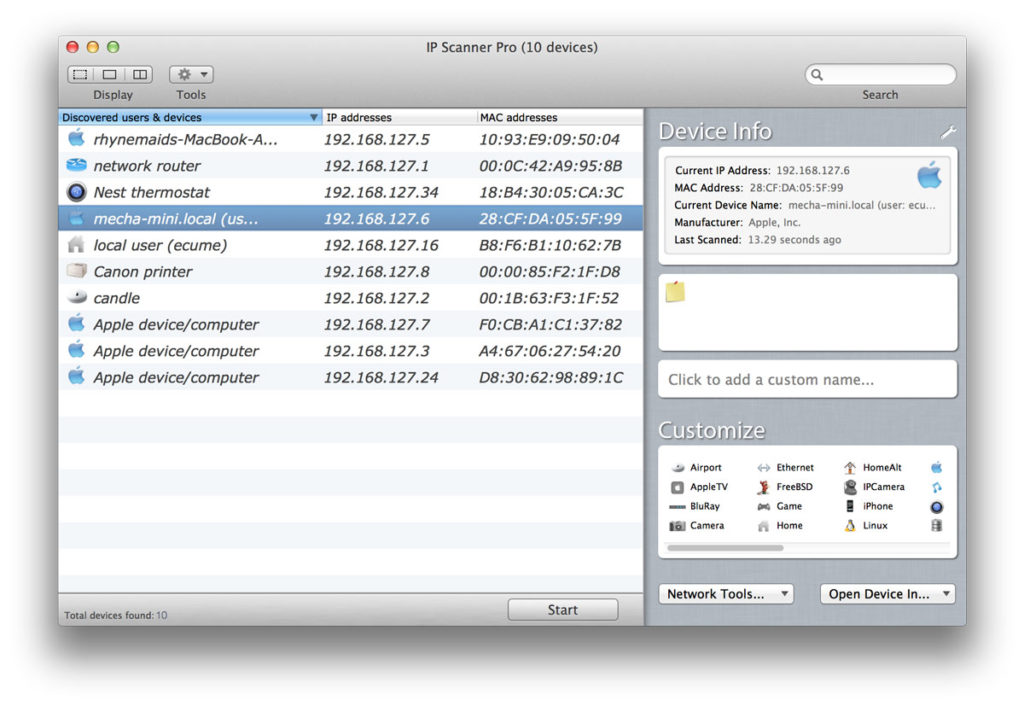
Created by developer 10base-t Interactive and optimized for Mac, this app is admittedly limited; the free version only supports 6 devices. Still, for small home networks, this number may be sufficient, and, as a taste of what could be possible with the expanded capacity of the Pro version, IP Scanner offers features many other free apps don’t have.
Perhaps most interesting is IP Scanner’s “cumulative mode” feature, which allows the user to track network changes over time. In this mode, network admins can see inactive devices that were once part of the network. This can help with troubleshooting in a variety of ways. Is this IP address now free for reallocation? Is this device supposed to be present, and something has gone wrong? IP Scanner takes some of the guesswork out of network fluctuations, making it possible to zero in on these questions and find answers.
Another intelligent feature is the tool’s whitelist capability, which allows users to filter out trusted devices. By culling the display in this way, users can stay aware of which devices are new and may be on the network without authorization, receiving automatic alerts to potential threats.
4. Engineer’s Toolset (Free Trial)
Next up is SolarWinds Engineer’s Toolset™ (ETS), a bundle of over 60 tools designed to discover, configure, monitor, and troubleshoot your network. This includes a slate of tools fulfilling the duties of an IP tracker or scanner, bolstered by myriad others in this holistic network management client.
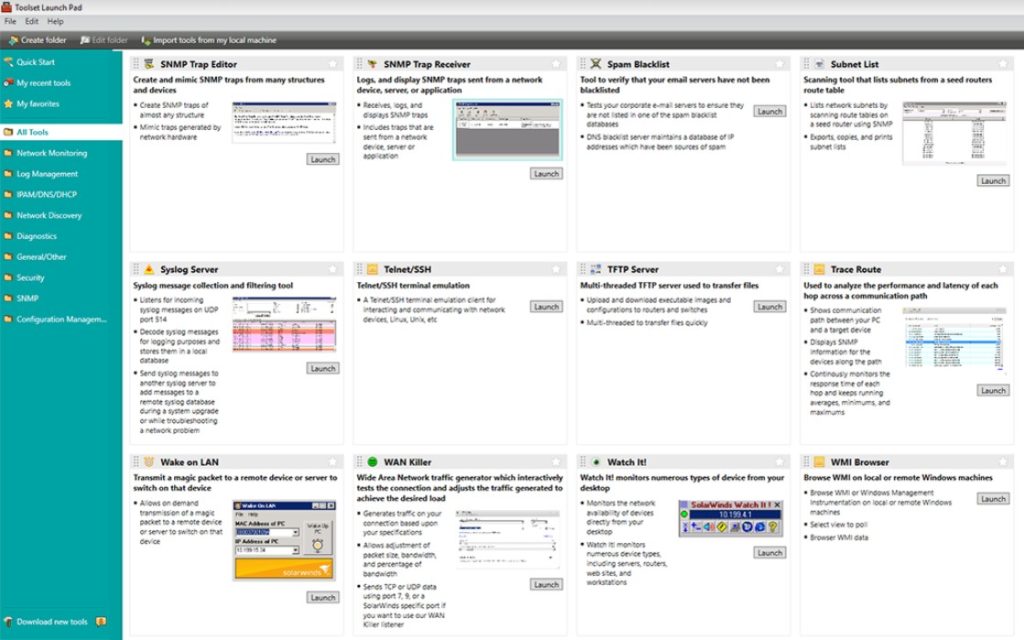
Some of the toolset’s key strengths are its convenience and birds-eye-view perspective of complex enterprise networks. SolarWinds ETS performs automated network discovery, allowing it to undertake clear network visualization—a capability not found in most free tools. With the automated discovery, the toolset displays the network in its entirety, mapping out switch ports, relating MAC to IP addresses, and identifying equipment.
To this end, ETS generates powerfully informative graphics for all IPAM concerns. Not only does the Ping Sweep tool provide a quick rundown of which addresses are in use and which are available for assignment, but it also locates the DNS name corresponding to each IP address. It supplements this data with graphs charting device response time.
Beyond scanning and mapping networks, Engineer’s Toolset makes reconfiguring the network for optimal performance a breeze. The Subnet Calculator at once scans subnets; generates the proper masks, size, range, and broadcast address of both classful and classless subnets; and acts as an IP address tracker, continuously monitoring the addresses in use within each subnet.
The DHCP Scope Monitor, meanwhile, monitors DHCP servers to push alerts when certain scopes are low on addresses and quantifies the number of dynamic IP addresses within the network. This is an incredibly important function when re-architecting a network or trying to avoid downtime, as it gauges whether the network is due to run out of addresses before a verifiable shortage arrives.
Further, the DNS Audit tool maximizes IP address efficiency through its ability to run forward and reverse DNS lookups to find any misalignment with host addresses and DNS records. This helps ensure if a device is using an IP address, the network reaps the rewards of having allocated that address.
Coupled with the innumerable other amenities of SolarWinds ETS, its network scanning and IP address tracking features go even further in preventing network catastrophe, identifying problems early, ascertaining root causes, and executing quick resolutions.
5. Network Performance Monitor (Free Trial)
SolarWinds Network Performance Monitor (NPM) is another fully loaded toolkit ready to scan networks for devices. Its network device scanner tool automatically discovers network devices; beyond that, NPM creates visual displays that delineate the connections between devices — automatically populating maps that clarify network topology. This is particularly helpful in the case of the dynamic IP address system, in which IP addresses (in addition to device count and relationship) are constantly in flux.
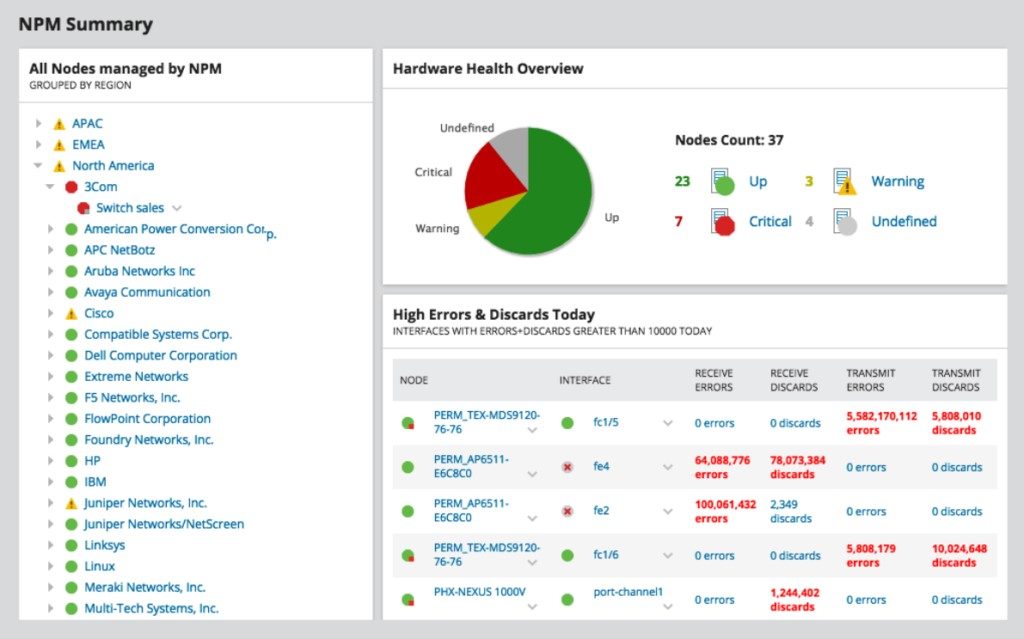
Network visualization in NPM goes far beyond the typical features of an IPAM tool. In fact, with SolarWinds NPM, users can customize dynamic network maps that display accurate topology and device performance metrics, juxtaposing device scanning and network performance management so that admins can more easily architect high-performing networks and intervene on specific devices when necessary.
6. SolarWinds User Device Tracker (Free Trial)
SolarWinds User Device Tracker (UDT) performs an IP address management role from a unique vantage point, looking more at the individual user in addition to network architecture. UDT is invaluable when it comes to granular network topology and equipment details. It automatically discovers and monitors layer 2 and layer 3 switches, and it constantly watches ports and switches, gauging response time, packet loss, CPU load, and memory utilization. It sends alerts as switches approach their capacity.
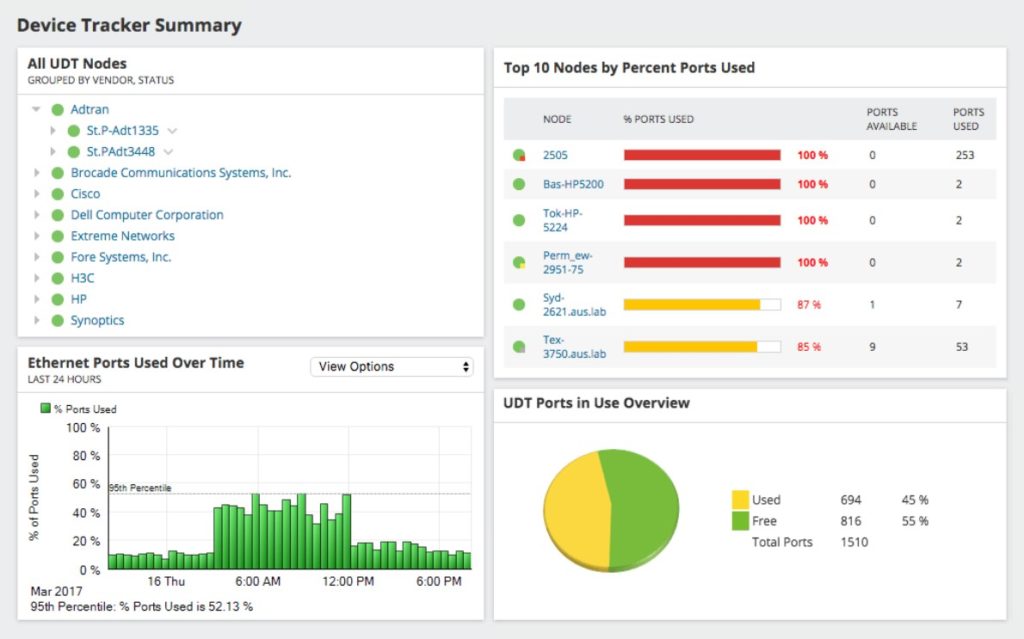
UDT serves a pragmatic function in this way through network visualization and performance monitoring. In addition, it provides enhanced visibility into network users and strengthens network security—an increasingly crucial consideration as networks grow more complex and organizational members each bring a bevy of devices, presenting more opportunities for breaches.
With SolarWinds UDT, admins can not only customize their own reports—vital for compliance—but they can also drill into device connection history and user login history. Most importantly, they can cut through the noise to identify any unauthorized users siphoning resources from their network or, worse, carrying out cyberattacks. The UDT whitelisting feature empowers admins to designate safe, known devices so it can push alerts when new and potentially dangerous devices come online.
The Importance of IP Addresses in Networking
Now that you have the best tool in place to scan, monitor, and manage IP addresses on your network, having a baseline understanding of how IP addresses work—including the differences between the addressing systems of IPv4 and IPv6—can also help protect the performance and integrity of networks. Let’s go into deeper detail about what exactly an IP address is, types of IP addresses, and how to assign IP addresses to devices.
What Is an IP?
The IP address exists to identify devices connecting via the internet, which is itself a network of other networks communicating via the standards delineated by the Transfer Control Protocol (TCP) and Internet Protocol (IP). The term “internet” in this sense is different than Local Area Networks (LANs) in that it’s decentralized—meaning no specific person or device has administrative privileges to impose controls on the web—and allows each internet-connected device to act independently online.
To achieve internet access, then, every device must have a way of identifying itself. Identification serves two primary purposes:
- It acts as a “return address” so all packets transmitted over TCP (all data transfers and communication exchanges, basically) can be verified.
- It allows other devices to find and communicate with the device in question.
Though accessing the internet quickly and easily is something most take for granted, it’s a process comprised of multiple steps. A user who wishes to reach a site on a computer or other device inputs the domain name (like www.dnsstuff.com) into their browser, which then contacts its designated domain name system (DNS) server to resolve the URL to an IP address. Once the device has the IP address, it can connect to the site and interact however it wants.
Because most networks, including LANs, virtual LANs, and Wide Area Networks (WANs), use the TCP/IP protocol suite to connect the devices in a given organization or location, the IP address system works similarly to ensure network devices can successfully send data to one another.
All IP addresses have both binary and dot-decimal notations for an address. The binary representation of an IP address is used to communicate with devices, while the translated dotted decimal format helps make it easier for users to understand and remember IP addresses.
What Version Is My IP Address? IPv4 vs. IPv6
Currently, there are two coexisting standards (also called versions) for formulating IP addresses:
- IPv4 (Internet Protocol version 4) – an IP address is made up of decimal digits and contains 32 bits or 4 bytes. Each byte constitutes an 8-bit field with decimals and a period, which is why some call IPv4 address nomenclature the “dot-decimal format.”
While this has worked well enough for quite some time, the 32-bit constraint means IPv4 only allows for variations or approximately 4 billion addresses. At present, the global number of internet-connected devices already far exceeds that threshold, at 26.66 billion. To compensate, many networks use both private and public IP addresses, so several devices within a local network may share a public IP address but have separate private IP addresses. A system called the Dynamic Host Configuration Protocol (DHCP) assigns private IP addresses within a network.
While this system has worked historically, it poses a couple of problems. First, it introduces an additional step in networking and increases administrative overhead. Second, if the DHCP and DNS server aren’t synchronized (or if multiple DHCPs are running at once, which admins should avoid), listed IP addresses can be incorrect or duplicated, causing transfer issues that can, in turn, hinder network performance. When two devices share a single IP address, they may not be able to connect to the internet or the local network at all. - IPv6 – developed to circumvent these complications. Four times larger than an IPv4 address, an IPv6 address contains 128 bits in total, written in hexadecimal, and punctuated by colons rather than periods. With more data allocated for each address, the IPv6 protocol creates many more IP address variations than IPv4, eliminating the need to assign public and private addresses, which can result in collisions. Since it allows for variations, the new protocol provides a good deal of room for IoT to grow. Because IPv6 is an evolutionary upgrade, it can coexist with IPv4 and will do so until the earlier version is eventually phased out. For this reason, IPv6 is also referred to as IPng — meaning “Internet Protocol next generation.”
So far, IPv6 addresses still represent the minority of internet traffic, but they’ve started to capture a larger portion. As of June 2019, around 29% of Google users accessed the site over IPv6, and around 38% of internet users in the United States have already adopted IPv6 with minimal latency rates. By transitioning to IPv6 over time, the internet should be able to allocate more individual addresses to devices, increasing both the number of hosts and the volume of data traffic it can accommodate.
What Is IPv4?
Each IPv4 address contains two crucial components: a network identifier and a host identifier. In this way, it’s much like a geographic address—the street gives people an idea of the neighborhood where a building is located, and the number isolates the building in question.
In an IPv4 address, the network identifier contains the network number, which, per its name, identifies the specific network to which the device belongs. The host identifier, or node identifier, is the collection of bits unique to the device in use on the network, differentiating it from other machines on the network and on the internet.
IPv4 Classful Addressing Basics
The number of nodes a network will need to support determines the exact structure of the IPv4 address, which is further classified into different address classes.
- Class A IPv4 addresses – If the first bit of an IPv4 binary address is 0, then the address is a Class A type. Class A is typically used in large organizations as it can generate millions of unique node variations. Class A has an IP address range of 0.0.0.0 – 127.255.255.255
- Class B IPv4 addresses – If the first two bits are 10, the IPv4 address is Class B. Class B can produce tens of thousands of node address variants and is primarily used in medium-sized networks. Class B has an IP range of 128.0.0.0 – 191.255.255.255
- Class C IPv4 addresses – All Class C addresses start with 110. Since Class C IPv4 address allocates one byte to the host identifier, this tier of IPv4 network can only support a maximum of 254 hosts. This is because a byte of data is equal to 8 bits, or 8 “binary digits.” With a bit limited to representing either 0 or 1, an 8-bit piece of data allows for a maximum of (256) variations. However, the host identifier “0” is reserved for the IP address designated to the network, and 255 belongs to the IP address designated to the broadcast address, leaving 254 network nodes for other devices. Class C has an IP range of 192.0.0.0 – 223.255.255.255
While Classes D and E also exist, Class D is used exclusively for multicasts and Class E not available to the general public.
Classful vs. Classless Addressing
Because of fears that the classful IPv4 addressing system was too quickly using up available address variations, the Internet Engineering Task Force developed the Classless Inter-Domain Routing (CIDR) system to allow for network prefixes sized between the 8-bit intervals instituted by classful networking. With CIDR, an IPv4 address doesn’t have a set composition defined by its class; it can, however, have a prefix (the portion specifying the network number or subnet ID) of arbitrary length. The size of this prefix determines the number of variations available to each network or subnetwork.
CIDR can work because of the variable-length subnet masking (VLSM) technique. Put simply, the subnet mask expresses in dot-decimal IP form how many bits in the IPv4 address belong to the prefix. For example, a CIDR with a prefix length of 4 (meaning the network number is only 4 bits, as opposed to a typical Class A length of 8) is, in binary, 11110000 00000000 00000000 00000000. The byte “11110000” numerically translates to 240, making this subnet mask address 240.0.0.0. Given this subnet mask, an admin knows the network can support devices—much more than a Class A IPv4 address.
According to CIDR notation, the length of the subnet mask (the number of bits used by the prefix) is expressed by a suffix composed of a slash and a number. So, given the IP address 192.168.1.0/24, a user would know the following:
- The prefix is 24 bits, or 3 bytes, in length, making it a Class C IP address
- Therefore, the network can support up to 254 devices
- The network address is the first 3 blocks, or 192.168.1
- The IP address is 11111111 11111111 11111111 00000000 in binary, translating to the subnet mask 255.255.255.0
What Is IPv6?
IPv6 addresses work in a similar fashion to IPv4 addresses, though they contain more data. Each hexadecimal number requires 4 bits, and each block consists of 4 hexadecimals. Each IPv6 address contains 8 blocks—128 bits total, which are, like IPv4, divided into network and node components. The difference between the two versions is IPv6 addresses don’t vary in composition; the network and node components are always of equal length, at 64 bits each.
The first 64 bits correspond to the network component, laying out the global unicast address (48 bits) followed by the subnet ID (16 bits). Essentially, this means that the first 3 bytes identify the network address used by internet routing to reach the proper network, and the fourth byte (configured by network administrators themselves) routes any communications to the correct internal subnet within the broader local network.
The last 64 bits make up the interface ID, which identifies the node within the network that internal network or external internet communications must reach. The interface ID is generated from the media access control (MAC) address, given by network interface card manufacturers and stored in the device hardware.
Although IPv6 addresses don’t have classes, the hexadecimals with which the address starts can inflect what type of network it is. Global addresses starting with “2001” are public, whereas link-local addresses starting with “fe80” and unique local addresses starting with “fc00::/8” or “fd00::/8” can channel communications internally, but not over the internet.
Ultimately, IPv6 incurs some inconveniences. Namely, infrastructure will have to transition between the protocol versions, and the addresses are significantly longer. But the protocol solves the most notable dilemma networking faces: a shortage of IP addresses.
With its expanded capacity to support network nodes, IPv6 doesn’t just offer “enough” addresses for now; indeed, it is equipped to generate more variations than we’ll (hopefully) ever need. The number is practically inconceivable in human terms. As one computer hobbyist puts it, that value (340,282,366,920,938,463,463,374,607,431,768,211,456) is equal to over 340 undecillion. Put another way, that amounts to 50 octillion IP addresses per human being, given a global population of 7.5 billion.
How to Assign IP Addresses
Finally, to round out our understanding, it’s worth clarifying how IP addresses are assigned to devices, and how this can affect network operation. There are two basic forms of IP address: static and dynamic.
In a static system, an administrator assigns the IP address and it doesn’t change with server updates, router reboots, or website changes. This understandably has its pros and cons. A static IP address can be relied upon to stay the same regardless of other infrastructure developments, meaning IT admins will never encounter a surprise when scanning for IP addresses. However, depending on the size of the network, the manual allocation of all host IP addresses can require a massive amount of time, tracking, and structuring. Especially given that static addresses can become incompatible with a system in various ways, choosing to exclusively use static addresses is largely inefficient and inflexible.
Nevertheless, there are several good reasons to opt for the static IP address system. The process of assigning a static IP address is lengthy and complicated, so it typically requires a professional. This constraint makes static IP addresses more suitable to a business environment, though they can add benefits to home networks as well. Static IP addresses are helpful when:
- You want to ensure a shared resource (like a printer or server) is always accessible to everyone on the network, no matter their device, by giving it an unchanging address
- You want to use devices incompatible with DHCP
- You want to avoid IP address duplications, which a faulty DHCP server can generate
- You want slightly improved network security and geolocation precision compared to a dynamic IP address system
Dynamic IP addresses, in contrast, are assigned by the DHCP server, eliminating the need for an admin to spend hours allocating addresses. As their name implies, dynamic IP addresses don’t stay the same over time—the DHCP doles out IP addresses to devices on a temporary lease. This automates many of the more irksome details of configuring an IP address system: without administrative oversight, the DHCP server can assign a unique IP address, a subnet mask, a gateway address, and other requisite reference information (like the address of the DNS server) to all devices.
The advantages of the DHCP system are obvious: it reduces administrative overhead and scales with the environment. It has its disadvantages, as well, notably regarding the temporary nature of the dynamic IP address. Although the network client can attempt to renew the same address repeatedly, its address is not guaranteed. Particularly when it comes to remote work, attempts to gain access to a distant device or network can fail without knowledge of its current IP address.
Additionally, within networks primarily reliant on DHCP but have defined a few static IP addresses for isolated devices, a DHCP server can generate a unique IP address that conflicts with an existing static one, or the DNS and DHCP servers can fall out of sync, causing some sites and devices to become unreachable. These potential hiccups have solutions—altering the DHCP scope to exclude static addresses in use; changing DNS scavenging settings to ensure the server purges old records and updates its data—but they require foresight and additional work.
Still, barring slight complications, a dynamic IP address system is the most reasonable solution for large-scale networks. While many enterprises may use a static IP address with their router for remote networking or internet security purposes, DHCP is an efficient, useful system for node address designation overall.
Positioning Your Organization for Success
Overall, regardless of network size, downloading tools can offset an IT department’s workload.
While free tools are adept at handling smaller tasks—like simply discovering active IP addresses and correlating them to MAC addresses—a diverse toolkit like those offered by SolarWinds IP Address Manager provides a comprehensive solution.
Whether you’re maintaining the security of a small network or looking to manage networks at the enterprise scale, the premium IP address management solutions from SolarWinds add the most value of any tool on the market. By performing data analysis, streamlining high volumes of data into insightful graphs, offering useful network visualization, and pushing security and IP address conflict alerts, SolarWinds software can help ensure networks remain in safe, peak-performance shape. Ultimately, through keeping tabs on the many rote and time-intensive tasks required by IP address systems, these robust tools free up administrators to apply themselves elsewhere.



