Routers are critical networking components that help segregate and manage business networks. Since routers handle a majority of the network traffic, router logs contain rich information pertaining to network activity. You can use this information to debug network issues, identify malicious activity, and remediate problems early on.
What Information Do Router Logs Contain?
Depending on vendors and additional functionality, routers logs contain different types of information, and logs produced by one router type or model may differ from other models. Moreover, some routers allow you to customize which events to log and which events to ignore.
In general, analyzing router logs helps you troubleshoot issues in the following types of scenarios:
- Routers maintain allow/deny lists that accept or reject data packets based on their source and destination. If you configure a router to forward data packets to private IP ranges only, it denies data packets with a public IP address as the destination. When a machine tries to connect to the open internet, the router denies the request. In general, multiple reasons can cause these issues and analyzing the network activity in the source machine might not help you find the exact problem. By analyzing the router logs, you can quickly determine the request was denied based on the allow/deny rules.
- Routers commonly allow setting protocol-based filtering to block or allow specific protocols. For example, if IPv6 is disabled on a router, it denies a data packet with an IPv6 address as the destination. In the past, you might have disabled it while initially configuring the router based on the requirements. You can identify this problem by searching for and reading this event from the router log.
- Address Resolution Protocol (ARP) binds MAC addresses to IP addresses. ARP spoofing and cache poisoning attacks are a problem as the protocol allows spontaneous reply, even if an ARP request is not sent. Because of this, some routers try to prevent ARP-based attacks and may accidentally block valid requests from your network components. You can understand why legitimate requests are blocked from the router logs and implement mechanisms to avoid blocking legitimate requests going forward.
- Routers may reject connections due to several other reasons. Again, the router logs contain the explanation for rejecting a particular connection, which you can analyze to understand the root cause.
Additionally, router logs contain access information detailing which components the router is communicating with and how. Monitoring router access logs helps detect malicious behavior or if the router is compromised.
Router Log Management
Routers generate large amounts of log data, and manually collecting and sifting through this information may not help troubleshoot time-sensitive issues. On the other hand, some vendors include additional capabilities in their routers, such as firewall, switch, hub, and other networking functionality types, making router log data more complex.
Moreover, routers usually delete the oldest log data when they’re out of local storage space to accommodate new log events. In some cases, the log data might not be appropriately saved due to power failures or unscheduled maintenance. Because of this, you should collect and store log data continuously at set intervals for troubleshooting, auditing, and compliance requirements.
In simple words, you need a comprehensive log aggregation and analysis strategy to centrally collect and store router log data and help search the log data for specific events and find patterns. You can use log management tools like SolarWinds® Papertrail™ to collect, store, manage, and analyze log data.
Log Aggregation
You should collect log data from routers and other network components, including host machines, firewalls, and network switches. Accordingly, centrally managing log data helps you correlate router log events with events generated by other components in your IT environment. Consequently, you can identify root causes more accurately and expedite remediation to prevent the known root causes from surfacing again.
Log Analysis
Analyzing logs helps you identify components affected by an issue and how the issue occurred. In addition, you can proactively identify progressively deteriorating network performance issues and fix them before they impact the broader IT infrastructure.
Some log analysis tools help you save frequent searches to perform searches and sift through data quickly. You can also automate saved searches to generate alerts for specific search results.
Simplify Log Management With Papertrail
Papertrail aggregates logs from various sources in your IT infrastructure, including routers, firewalls, host machines, databases, and web servers. It accommodates multiple log formats like syslog, text log files, Windows events, etc. Papertrail parses and indexes log data to bring uniformity and facilitate lightning-fast searches.
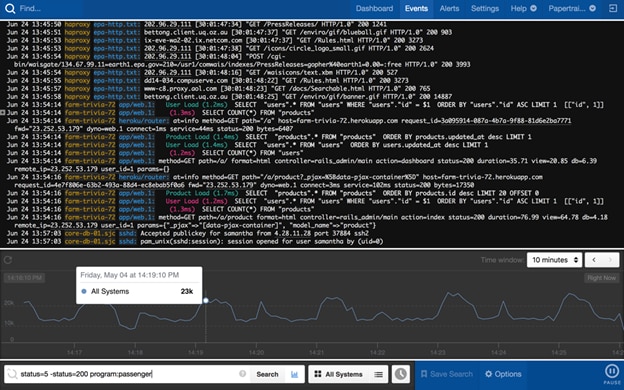
Papertrail is cloud-based, straightforward to configure and manage, scales as your log volume grows, and stores archived data as long as you need. You can also assign read-only or full log access to technical staff.
Papertrail allows you to save search queries instead of manually writing a commonly used query every time you need to search. Moreover, you can integrate Papertrail with SolarWinds AppOptics™ APM to attach log data to distributed traces generated from application performance monitoring. This enhances your visibility and understanding of network and performance issues and helps you identify root causes more accurately.
Give Papertrail a try and opt for its free plan here.
