There are countless tools out there to help you monitor and manage the users and programs within your system, so you can prevent ransomeware attackers from striking. I’ve rounded up some of the best anti-ransomware tools out there to help you avoid sifting through the noise. My favorites are Security Event Manager or Patch Manager—each tool has its own focus, but both address crucial aspects of ransomware prevention.
Feel free to jump ahead or continue reading:
Best Ransomware Protection Programs
- Security Event Manager
- Patch Manager
- Bitdefender Antivirus for Mac
- Check Point ZoneAlarm Anti-Ransomware
- Webroot SecureAnywhere AntiVirus
- CryptoDrop Anti-Ransomware
- Remote Monitoring & Management
Prevention! The Best Ransomware Protection
What Is a Ransomware Attack?
Ransomware encrypts files and presents companies with a mountain of meaningless text, paralyzing their ability to access the critical information they need to operate successfully. While these attacks are nothing new, they’re growing in popularity as cybercriminals develop more ways to bypass antivirus software and manipulate their way into your system.
IT pros who want to protect their company’s information and avoid paying thousands of dollars in ransom should consider implementing ransomware protection software.
Types of Ransomware Attacks
Ransomware is nothing new. For more than a decade this vicious form of malware has been used by cyber attackers to encrypt files, or sometimes even entire hard drives, and demand payment in return for the key needed to decrypt the files. This form of attack has grown in popularity as more and more companies digitize their real-time data and turn to cloud storage solutions, like OneDrive and Dropbox, to store their sensitive files. Pair this with the rise in anonymous payment systems, like Bitcoin, and you’ve got a perfect environment for attackers to strike.
For many years, Cryptolocker was the most dangerous ransomware perpetrator out there. It was often able to slip into a system unnoticed and create copies of itself that persisted even after safe mode reboots. Cryptolocker was eventually defeated by an international group of security agencies, but its methods continue to live on in other ransomware groups.
Many ransomware threats today take on several forms. Some of the most common ways they can infiltrate your system include:
- Infected Emails: Malware-infested emails disguised as legitimate messages from trusted users and colleagues within a domain often contain links or PDFs that, when opened, infect your system with malware.
- Fake Downloads: Hackers can create imitation banner ads, downloads, and popups on otherwise trusted websites, enticing users to click. If a user takes the bait, they’re opening the door for ransomware infection to enter.
- FBI Impersonation: Some hackers attempt to trick users into believing they have a committed a cybercrime and therefore their files have been encrypted. As a penalty, the FBI impersonator tells the user they must pay a fine (often in the form of Bitcoin) if they’d like to regain access to their files and continue operating.
A ransomware attack typically targets a user’s desktop or documents folder (these are the easiest to access) then spreads its encryption capabilities to lock off access to critical files. Attackers often request a “reasonable” amount from the victimized company—around $10,000—in exchange for the decryption key. This amount isn’t so large that many companies will instantly deny it, but it’s substantial enough to provide attackers with a steady stream of income. While any company can be mercy to ransomware attack, SMBs, healthcare institutions, and public service organizations are often targeted.
Best Ransomware Protection Programs
Luckily, there are several ransomware protection tools on the market to help keep your company’s files, devices, and money safe and secure. Some of these rely on regular backups to protect personal data, others implement bait files, and some use behavior-based detection to ward off attackers. There are even those that offer a unique combination of these techniques and more. I’ve rounded up the best anti ransomware tools out there to help you find the right fit for your business.
Of the ransomware protection tools on the market currently, SolarWinds Security Event Manager (SEM) is the one I find myself recommending the most. The platform provides a birds-eye-view of all network and user activity, so you can collect, consolidate, monitor, and analyze your log file data from servers, applications, and more in a single place. This security software is one of the most comprehensive ransomware prevention services on the market.
With its privileged access management capabilities, you can ward off attackers who prey on privileged accounts, by monitoring when privileged accounts are being used, how they’re being used, and from where. The tool will alert you immediately if a forced attempt to a privileged account is made. SolarWinds SEM takes this monitoring a step further with built-in cybersecurity intelligence feeds of known malicious IP addresses and attack vendors. These feeds are continuously updated with community-sourced data and research to help you stay ahead of new attack methods.
But the best part about SolarWinds SEM? The software even offers automated threat remediation. That means automated responses are generated that can block infected IP addresses, change user privileges, and disable accounts, all without you having to press a button. This can stop an attacker in their tracks. There is a possibility to try it for free.
Failing to stay on top of patches causes grief at companies worldwide. If your software and system aren’t updated, it’s all too easy for bad actors to find a way in. So, if your patching responsibilities are slowing down your workflow, it’s time to look at SolarWinds Patch Manager.
Keeping track of what got patched and what still needs to be patched can be overwhelming, especially with new patches coming out daily. SolarWinds Patch Manager automates this process on servers and workstations to decrease security risks and free up your workload for other crucial tasks. You can try it for free.

Bitdefender Antivirus for Mac is the best ransomware protection for Mac users. The software comes equipped with a suit of ransomware protection capabilities, including the power to block unauthorized attempts to manipulate files within protected folders, protect Mac Time Machine backups so your extra files remain secure, and block malicious URLs and adware that can veil a ransomware attacker. It also uses behavior-based threat detection to spot ransomware activity early and protect your documents form encryption.
Some users have expressed frustration with Bitdefender Antivirus for Mac’s traffic light and autopilot capabilities, but the software has taken active steps to remedy these issues. The software has earned some impressive scores in independent lab testing and is a top contender among the MAC anti-ransomware tools out there.
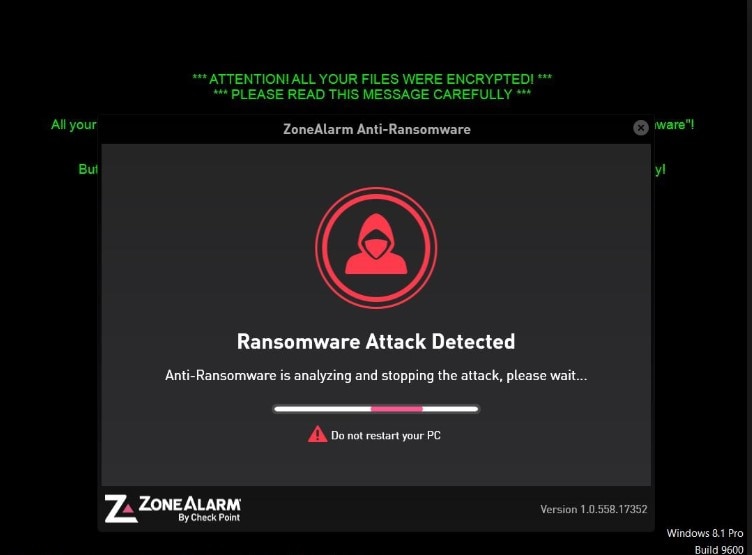
Check Point ZoneAlarm Anti-Ransomware is a very effective ransomware tool on the market today. It relies on the use of bait files placed in commonly targeted folders to entice ransomware attackers. As soon as one of these bait files is modified in any way, the software jumps into action and closes the infection down before it has the chance to do any damage to real files and folders. ZoneAlarm Anti-Ransomware tool also monitors network activity and has proven its power to repair and recover files that have been affected. This is a big bonus for those times when an attacker slips through the cracks. Its intuitive interface is another favorite element for many users.
One thing to watch out for—the software has been known to routinely encrypt, and then decrypt, some files. This glitch doesn’t cause any harm, but some users find it prohibitive.
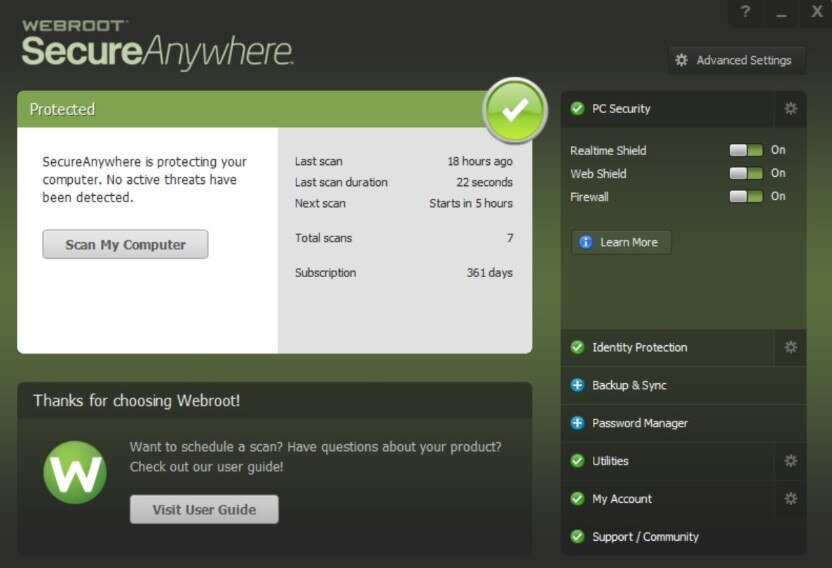
Webroot SecureAnywhere AntiVirus software is an extremely well-rounded product that uses behavior patterns to detect not only ransomware attacks, but any form of malware looking to cause harm to your system. It’s smart enough to know the good programs from the bad and has the capability to closely observe any suspicious activity. If a program seems questionable, it prevents it from connecting to the internet and logs every action it takes. By logging this data, Webroot SecureAnywhere AntiVirus has the power to undo any action conducted by the program if harm is caused. However, this function is limited in scope due to the size of the software’s database.
-
CryptoDrop Anti-Ransomware
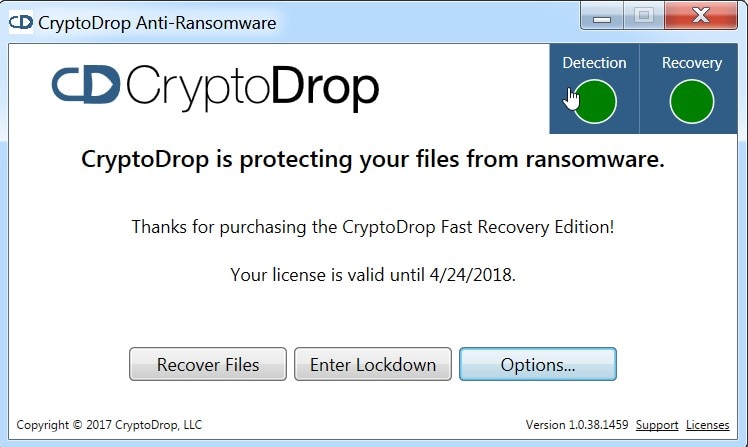
Like many of its counterparts, CryptoDrop Anti-Ransomware uses behavior-based detection to stop ransomware attacks in their tracks. The software also makes regular copies of your sensitive files and locks them away in a private, hidden folder. This ensures you have an extra set of those must-have documents if you do find yourself facing a pile of encrypted files because of ransomware. In laboratory testing, CryptoDrop Anti-Ransomware was able to defend against most, but not all, targeted attacks. The biggest con with this all-around strong product? It only protects the files you specify.

If you’re looking for a holistic tool that provides a robust feature set for helping protect against a ransomware infection and more, look no further. Remote Monitoring & Management (RMM) is built for managed service providers and can help you protect your clients’ sites and respond to potential threats quickly and decisively.
RMM includes Endpoint Detection and Response (EDR) tool, which analyzes files in real time and uses machine learning to detect and neutralize attacks. You’ll also get access to an antivirus software that updates constantly to respond to the latest threats. Plus, in the event of a successful attack on one of your client’s sites, RMM includes a backup and recovery tool so their data and content can be restored quickly.
Prevention! The Best Ransomware Protection
Once your system has been infected by ransomware, removing it with an antivirus update is pretty straightforward, but getting your encrypted files back? That can be a lot harder. That’s why ransomware prevention is the best tactic. While some methods will warrant manual effort, others can be implemented with the help of ransomware prevention software. Here are a few of the prevention practices you should be implementing:
-
- Education: Regularly inform employees about common ransomware schemes out there. Let them know what to look for, what types of links and emails to avoid, and what they need to do (contact you) if something seems suspicious. Users within accounts receivable, marketing, and management are a ransomware attacker’s primary target, due to the large number of emails they receive daily.
- Backup: Backing up your folders should take two forms—offline and online. Having a secure, cloud-based backup of folders is a great first step if the originals are infected. However, many ransomware programs are becoming more and more advanced and have started to intentionally seek online backups. Having physical backup of critical folders, whether in the form of a hard drive or some other media, will help ensure your business can quickly get up and running after an attack.
If you’re an MSP, you’ll also be expected to handle backups for all your clients. The N-able Backup solution makes this easy. It uses cutting-edge encryption to provide security, while also giving you the tools you need to streamline backup, storage, and restoration for your clients. - Updates: Always make sure you are using the most up-to-date version of software on your systems. Updates ensure new patches are put into place that can minimize or eliminate pre-existing vulnerabilities. Without these patches, your software is susceptible to several tried-and-true ransomware attempts.
- Monitoring: It’s important to keep a close eye on log and event management so you can quickly detect suspicious activity. This can be a time-consuming process, but there is ransomware protection software out there that capitalizes on automated, real-time, and behavior-based monitoring capabilities to keep you abreast of potential threats.
- Privilege: Not every user needs administrator-level access folders. Practice the principle of least privilege to ensure users are granted the minimal level of access they need to perform their day-to-day responsibilities. This isn’t about not trusting your employees, it’s about malware protection and limiting the scope of damage if an attack occurs.
- Email: Many different types of attacks arrive via email, and a simple spam folder won’t provide much protection against ransomware. For managed service providers, the N-able Mail Assure solution can help deal with infected emails quickly and efficiently. It offers advanced threat protection for both inbound and outbound emails, using real-time monitoring and pattern recognition to spot the latest attacks and stop them in their tracks. Plus, it can be used to protect hundreds of client sites and networks simultaneously.


