Staying cyber secure is essential in any modern business. Unfortunately, any system with a human element is going to include inherent weaknesses that make maintaining a secure posture more difficult. Intrusion detection systems have become particularly important in recent years.
No matter how strong you make your user access policies, bad actors are always going to be able to find ways around them. Even when you take every possible precaution, there are always new ways to trick unsuspecting users into disclosing access credentials to gain entry into your system. Once bad actors have access, they can occupy corporate systems for years without being detected.
That’s where an intrusion detection system (IDS) comes in. They are specifically designed to root out these kinds of attacks, called Advanced Persistent Threats (APT). In this piece, we’ll answer the question “What is IDS,” cover the different types of IDS, and dive into HIDS before discussing the top intrusion detection systems. If you want to skip ahead to the products, you can do so here:
What Are IDS and IPS?
IDS, or an intrusion detection system, is a software application designed to monitor your network traffic for suspicious activity, issuing alerts when it discovers any such activity. Typically, the system will either report malicious violations or ventures to an administrator, or it will centrally collect the information using a security information and event management (SIEM) system.
IPS, or an intrusion prevention system (sometimes called an intrusion detection and prevention system) also monitors network traffic and system activities for any malicious activity. It is often viewed as an augmentation of intrusion detection systems. However, there are some key differences between the two systems.Unlike IDS, IPS:
- Are placed in-line and they can actively block or prevent detected intrusions.
- Can take additional actions including sending an alarm, resetting a connection, dropping detected malicious packets, or blocking traffic from the offending IP address.
- Can defragment packet streams, mitigate TCP sequencing issues, correct cyclic redundancy check (CRC) errors, and clean up any unwanted transport and network layer options.
Types of Intrusion Detection Systems
There are five main types of IDS.
- Host Intrusion Detection System (HIDS): HIDS run on independent devices or hosts on a system, monitoring the incoming and outgoing packets for that device and alerting the administrator if malicious activity is detected. The system works by taking snapshots of existing system files and comparing them with the previous snapshot. If it sees the analytical system files were deleted or edited, the HIDS sends an alert to the administrator to investigate.
- Network Intrusion Detection System (NIDS): NIDS are set up at one specific point in your network to examine passing traffic from your devices. It observes traffic on the subnet and matches the information on those passing subnets to its collection of known attacks. If an attack or abnormal behavior is observed, the system alerts the administrator.
- Protocol-Based Intrusion Detection System (PIDS): PIDS is made up of an agent or system that resides at a server’s front end, controlling and interpreting the protocol between the server and a user or device. The goal is to protect the web server by monitoring the HTTPS protocol stream and accepting the related HTTP protocol.
- Application Protocol-Based Intrusion Detection System (APIDS): APIDS is made up of an agent or system that usually resides within a group of servers. It monitors and interprets the communication on application-specific protocols to identify intrusions.
HIDS — Host-Based Detection Explained
Host Intrusion Detection System, or HIDS, is an intrusion detection tool focused on monitoring logs to identify suspicious behavior. Storing and searching through logs to find signs of intrusion is a great way to identify advanced persistent threats (APTs), but keeping track of all the logs coming from all your applications can quickly become overwhelming and drain your resources.
HIDS software monitors the log files generated by your applications. It creates a historical record of activities and functions, making it easy to quickly search through your logs to find any anomalies or signs of intrusion. HIDS tools come with automated detection features designed to save you from having to sort through the logs yourself. HIDS use a combination of preset and customizable rules and policies to search through log files and flag anything that seems like it could be indicative of malicious behavior.
Host Intrusion Detection Systems (HIDS) use two key methods:
- Anomaly-based detection, which searches through your logs for signs of irregular or unusual activity caused by users or processes.
- Signature-based detection, which performs scans of your log data, monitoring it for patterns that could indicate the presence of an intruder.
Recommended Intrusion Detection Software, Windows
1. SolarWinds Security Event Manager
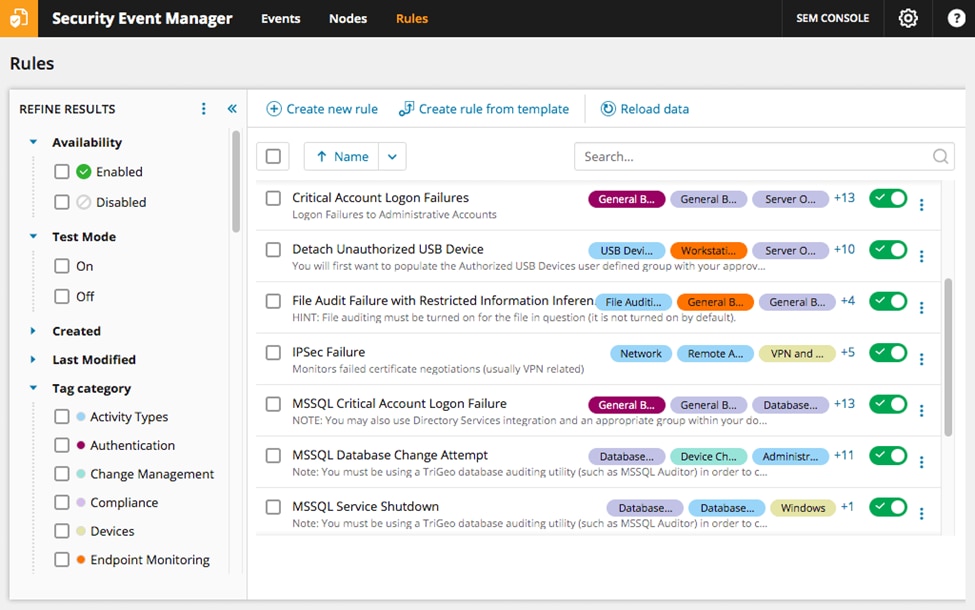
SolarWinds Security Event Manager (SEM) is a HIDS with a powerful lineup of automated threat remediation tools designed to keep bad actors out while saving you time and energy. SEM comes with helpful log management features built to make monitoring, forwarding, backing up, and archiving your log files simple. It comes with built-in storage and transit encryption, so your log files are safe.
SEM is a great example of an intrusion detection system. It can monitor your log files—including the ones that are still open—for new records. Whenever a warning condition is detected, the tool can raise an alarm. The solution’s analysis tool enables you to check on data integrity and spot intrusion manually. This visibility delivers an additional sense of security when it comes to keeping bad actors out.
But you don’t need to perform those manual checks if you don’t want to. SEM’s centralized log analysis system pulls and analyzes data from systems across your network to create a cohesive monitoring environment where the tool can more easily detect potential APT activity.
Templates let IT administrators get started using SEM without needing to do a lot of customization. The tool also offers significant opportunities for customization for those who want it. It can run audit reports for data security standards including HIPAA, PCI DSS, SOX, and more.
You can try out a fully-functional version of Security Event Manager free for 30 days.
2. ManageEngine Event Log Analyzer
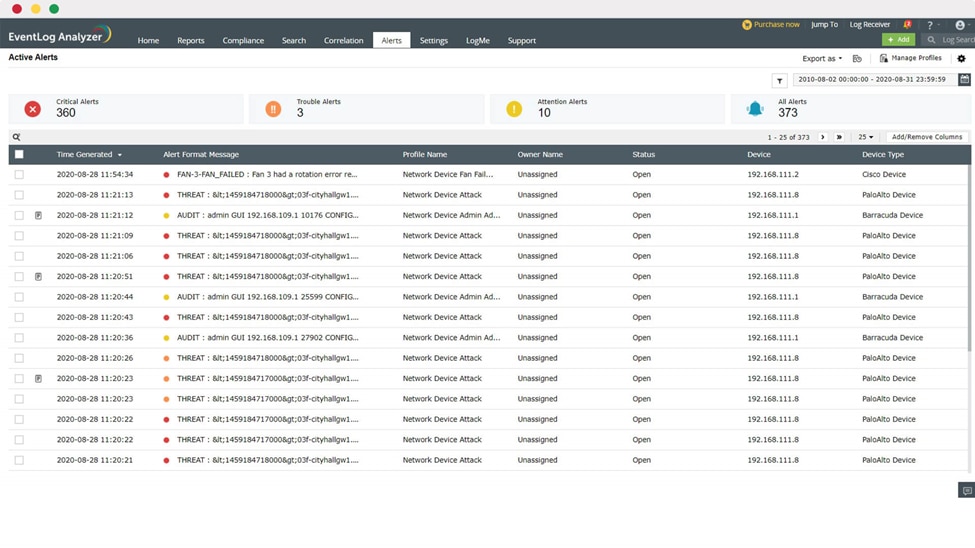
ManageEngine Event Log Analyzer is another great, comprehensive security application offering both HIDS and NIDS capabilities. The tool centralizes your metadata and logs in a single location and, if it detects that any of your log files have been inappropriately altered, it enables you to restore the original log files from a backup automatically. Like Security Event Manager, Event Log Analyzer uses encryption to protect your files. It also uses compression to protect the files and requires authentication for access to log files. When the tool detects potential intruder activity based on your logs, it can send alerts across multiple channels including email and SMS.
Event Log Analyzer has a customizable dashboard. You can create different screens and tailor your data collection to align with what’s most important to you for maintaining your organization’s data security standards. And, again like SEM, the solution offers compliance reporting for data security protocols including PCI DSS, FISMA, GLBA, SOX, and HIPAA.
Try ManageEngine Event Log Analyzer free for 30 days.
3. OSSEC
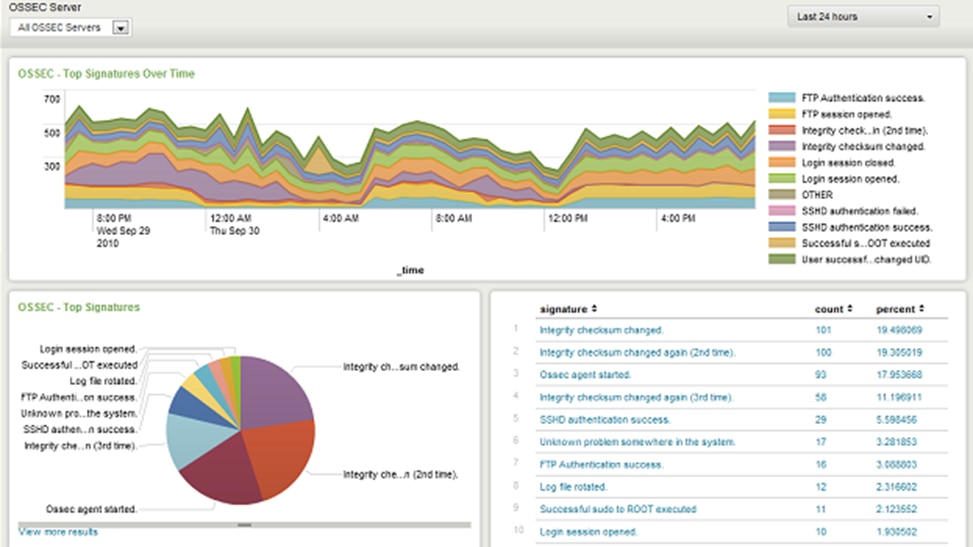
As far as an open-source intrusion detection systems goes, OSSEC is a stand-out. Technically a HIDS, OSSEC offers a few system monitoring features more common in a NIDS. OSSEC is extremely efficient when it comes to processing log file data, but it doesn’t come with a user interface. Luckily, you can get around this by using an open-source dashboard like Graylog or Kibana.
OSSEC can organize and sort your log files and before using anomaly-based detection policies and strategies to identify potential malicious activity. Since it’s open-source, you can easily download predefined threat intelligence rule sets created by community users who also have OSSEC installed. If you ever need help with the tool, you can again turn to the community or you can purchase a professional support package from Trend Micro (the company that produces OSSEC).
Download OSSEC (or OSSEC+, which offers even more features) for free here.
4. Splunk

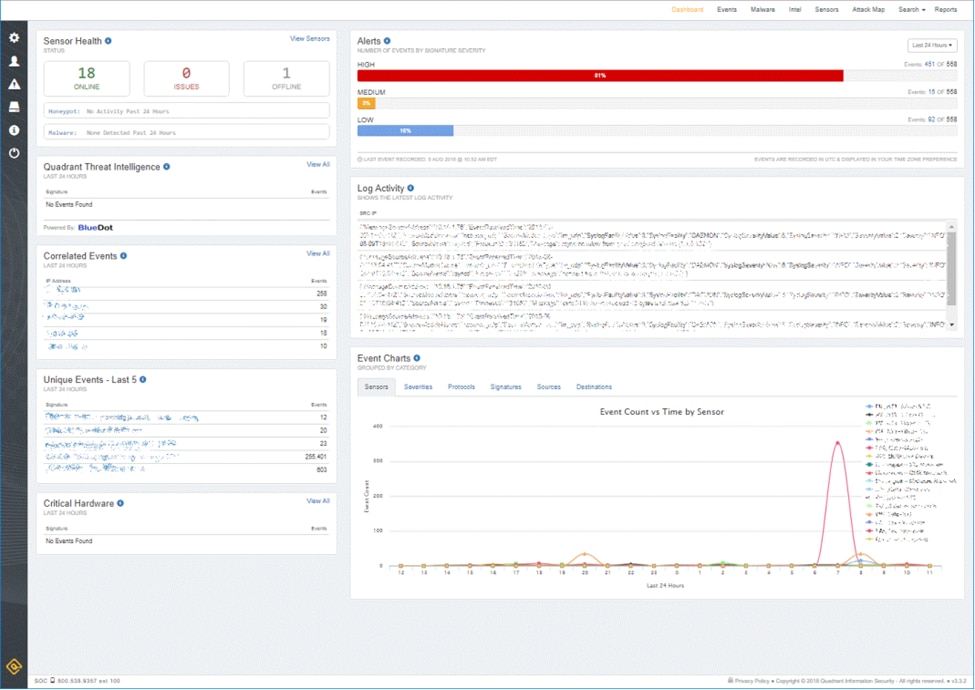
Splunk is another IDS with a free base-level application as well as several paid options with additional features. The free version of Splunk offers anomaly-based intrusion detection as a HIDS option. If you’re looking for additional features, you can check out the paid versions of Splunk. They deliver automated workflow features to respond right away to any detected threats, making them more of an IPS solution than a simple HIDS.
Unlike OSSEC, Splunk offers a great user interface and a dashboard with useful visualizations including pie charts and line graphs. All versions of Splunk also come with a built-in data analyzer that lets you view your records as well as summarize, sort, and search through them.
Splunk include can leverage behavior analysis to detect threats that aren’t identified through your logs, offers easy prioritization of events, and is very enterprise focused. On the other hand, the biggest drawback of Splunk for smaller organizations is its precise enterprise focus. The paid versions of the tool can be cost-prohibitive for smaller businesses. Additionally, Splunk has a steeper learning curve than other products on this list because it uses its own custom Search Processing Language (SPL) for queries.
Check out free trials and downloads of Splunk here.
5. Sagan
Sagan is another free tool that uses both anomaly-based detection and signature-based detection strategies to identify signs of potential malicious behavior. Sagan is customizable, letting you define what automatic actions you want the application to engage in when it detects a potential intrusion.
Sagan comes with a few cool tools other HIDS don’t offer. The most exciting is perhaps its IP geolocation feature, which creates alerts if the tool detects activity from multiple IP addresses stemming from the same geographical location.
Sagan can only be installed on Mac, Linux, or Unix operating systems, but it can still collect Windows event log messages. This makes it a great solution for organizations running other systems as well as Windows.
You can download Sagan for free here.
Choosing the Best Network Intrusion Detection Solution
There are a lot of different options when it comes to intrusion detection tools for Windows. Deciding which tool is best for you depends on the size of your network, the operating system on your log servers, and how hands-on you want to be in the intrusion detection process.
If you’re looking for a top-of-the-line Intrusion Detection System solution, I think you can’t do better than SolarWinds Security Event Manager (SEM). SEM is a powerful HIDS software that functions as a Windows IDS while also collecting data from Unix and Linux systems. It offers an impressive lineup of automated threat remediation tools while also offering log management features. You can try out SEM free for 30 days to see if it’s a good fit.

